reme Part 1 - CSCG
Category: Reverse Engineering
Difficulty: Easy
Author: 0x4d5a
Reconnaissance
Here are the files if you want to try it for yourself: reme-1.zip
Reading the description we can find that we need a windows environment with .NET Core Runtime 2.2 installed
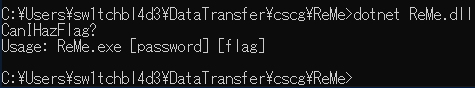
After getting that up and running I executed the file:
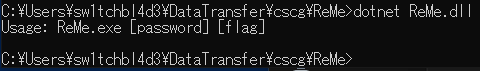
So we need a password, let's see if we can find one!
Exploitation
My tool of choice for .NET apps is dnSpy.
Does what it should, and can edit and recompile the code.
Just what we need.
After installing dnspy just open it and drag the ReMe.dll in.
Then on the sidebar browse to the main method like this:
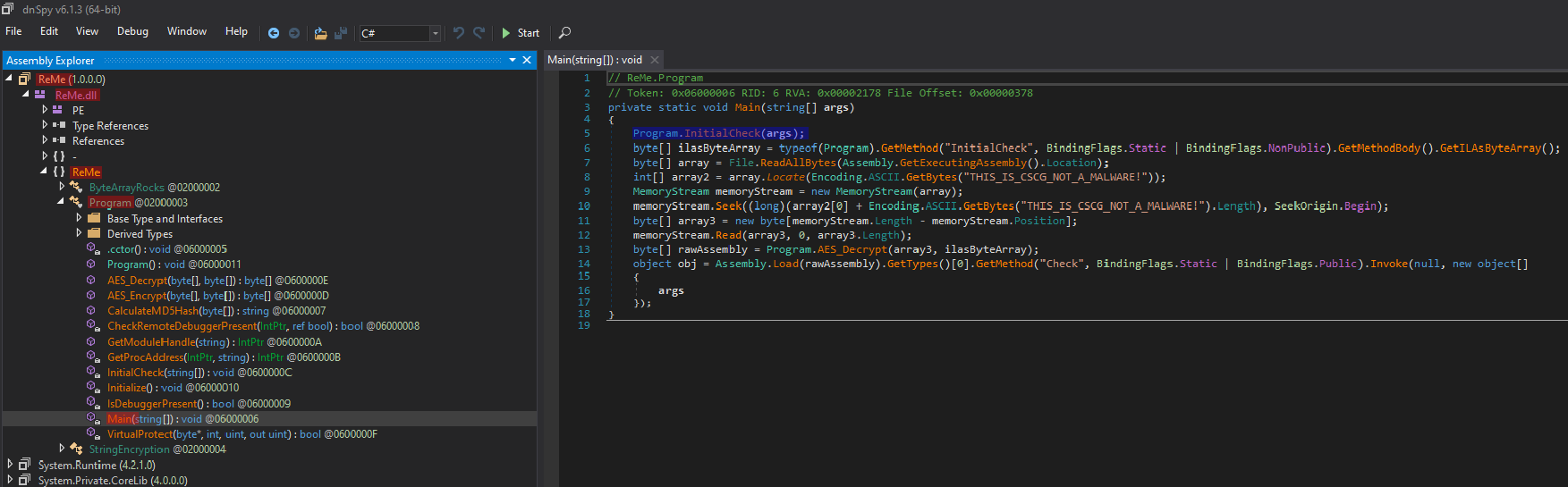
Follow the points I marked red, and you'll find yourself in the main method.
The first thing it executes is InitialCheck, lets check that out!
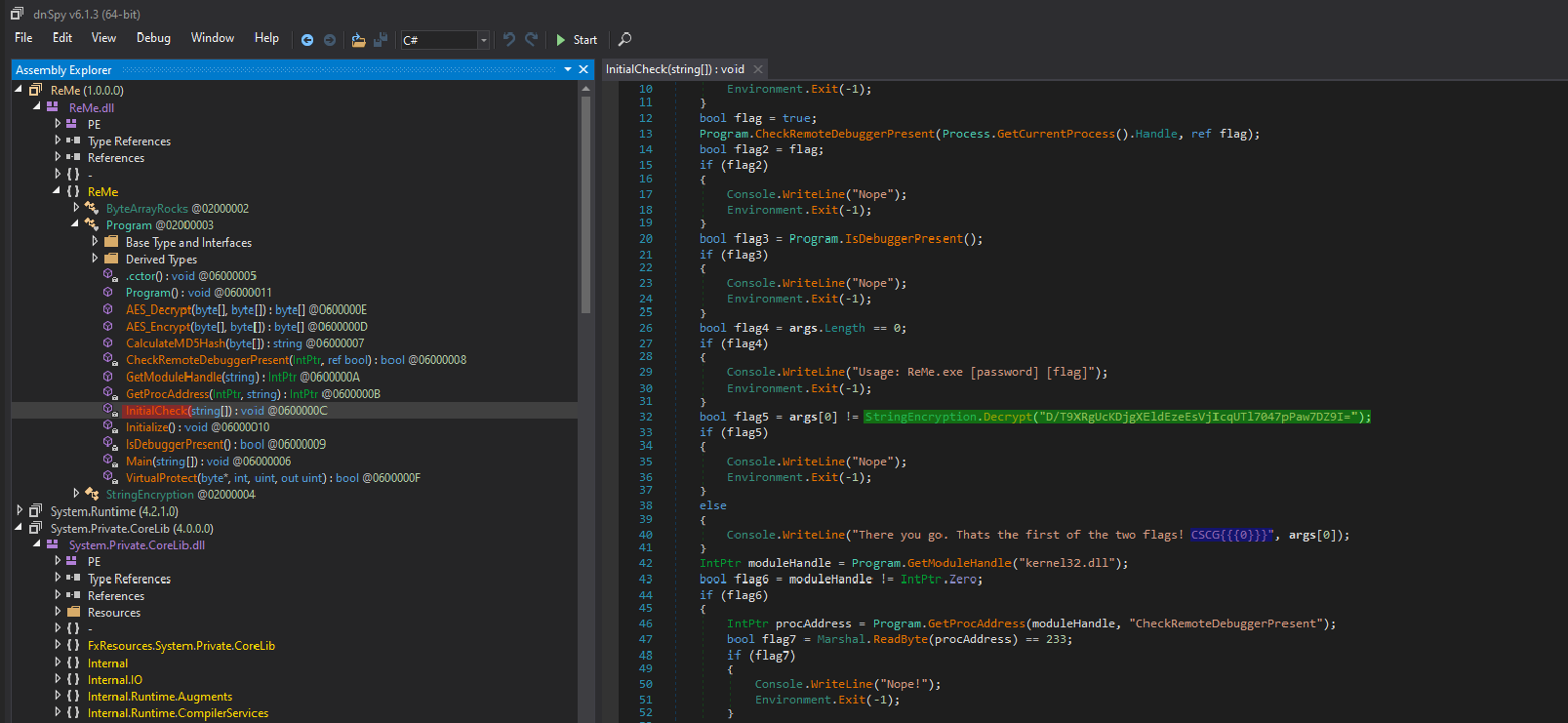
Here we can see that it compares the first argument with the result of that String.Decrypt() function.
But we can't see the flag (blue).
So we need to find out how we decrypt that Password.
Shouldn't be too hard.
I've gone back into main, and rightclicked.
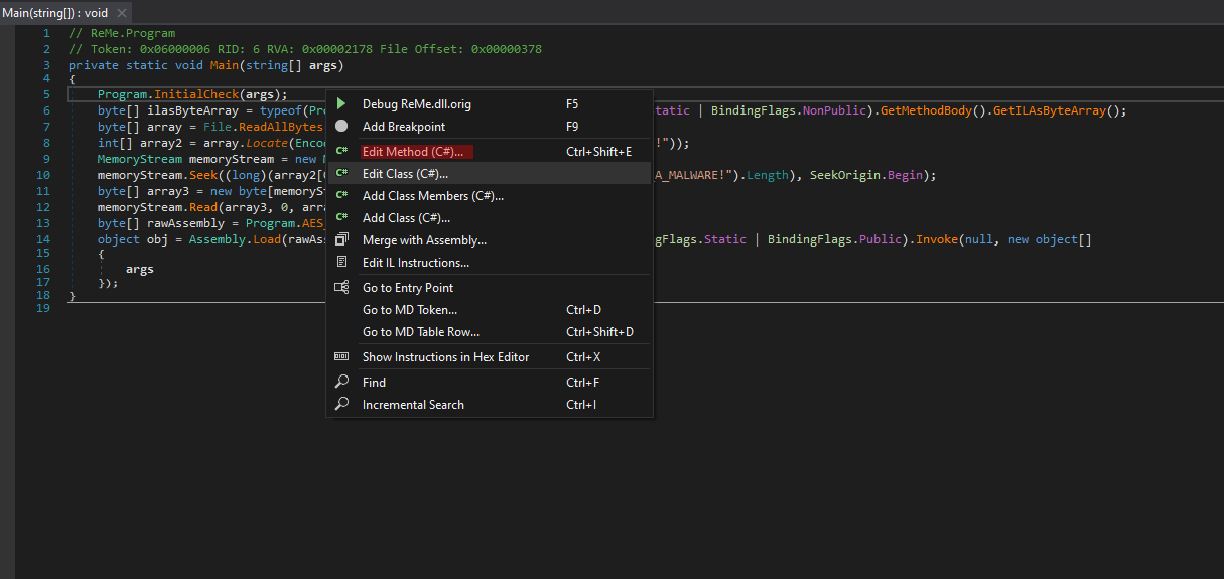
There you can click Edit Method (C#)...
Then you get the Code.
And how do we get the decrypted Password now?
By printing it!
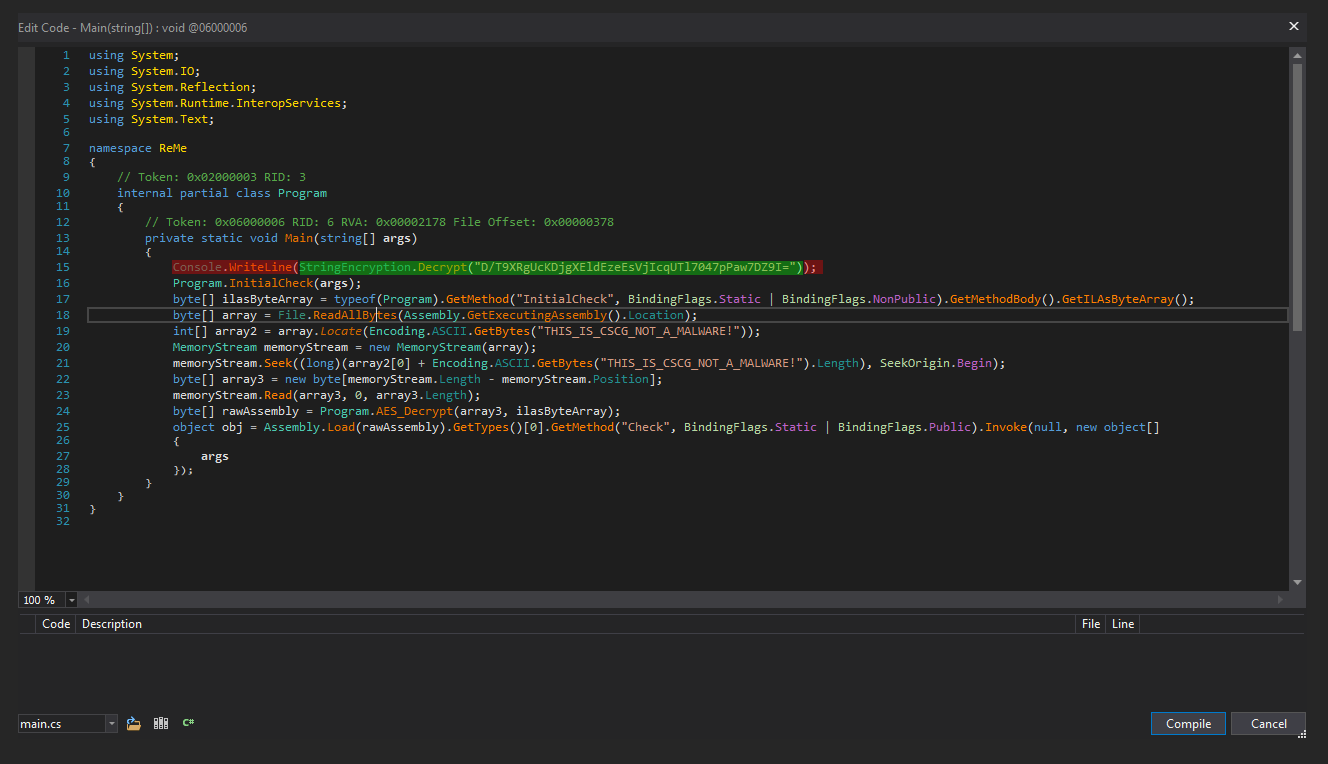
Just add a Console.WriteLine() and let it print the decrypted String!
After you put that in, just click Compile and it's in!
After that you want to save the edited dll.
Before that I advise you to make a backup of the file (or redownload it after getting the first flag).
In the upper-right corner, click File
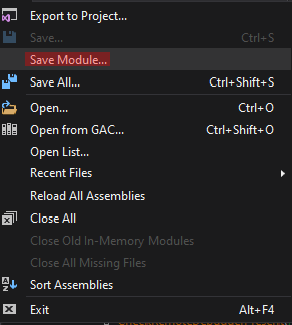
And click Save Module...
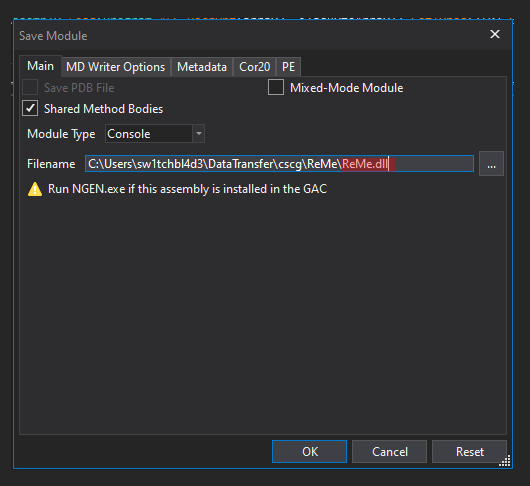
The Name MUST be ReMe.dll, otherwise it wont start.
So overwrite your copy of ReMe and download it again later, or put the modified file into another dir and copy the json-junk with it.
Anyway, click OK to save the file. After that you can close dnSpy.
Then open another shell (cmd/powershell, your choice), and open the file.
And Bingo! CanIHazFlag? is printed on the screen!
Now get the original ReMe.dll back, and use the password aaand.....
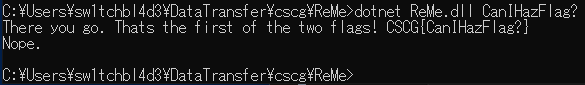
There's the flag! CSCG{CanIHazFlag?}
The nope after that is because you only specified one parameter, but it needs two, but thats part of ReMe2!
Mitigation
As I say in every RE-Challenge, Obfuscation won't help. Sure, it'll postpone the search for a bit, but at some point someone's gonna get it.
That's why I recommend using Hashes like SHA-512 for obvious reasons.
Good Hashes can't be reversed (at this point of time), and are just the most secure way out.
~sw1tchbl4d3, 07/03/2020 (dd/mm/yyyy)